How It Works
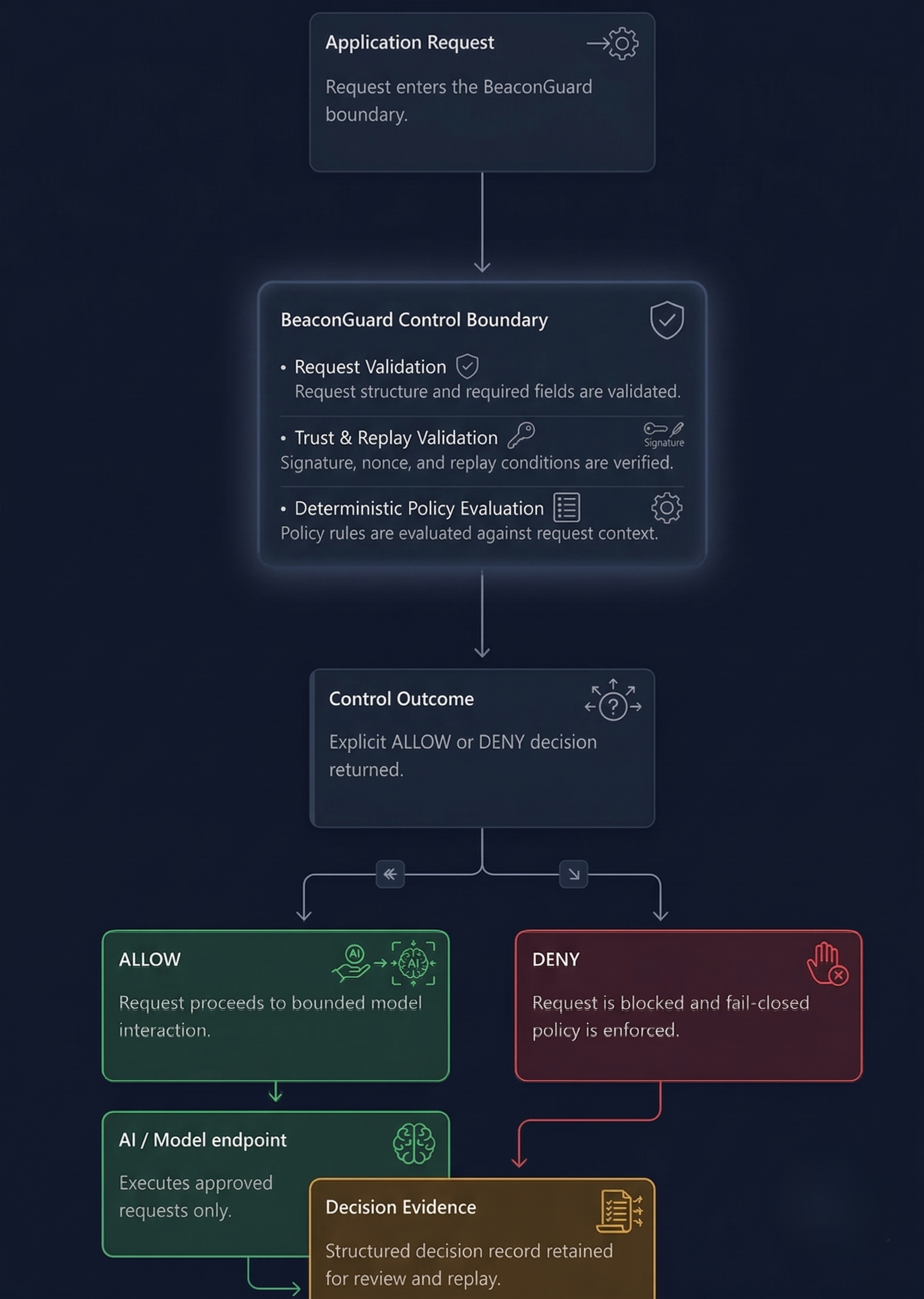
BeaconGuard evaluates each outgoing AI request through a deterministic control boundary before the request proceeds to model execution.
Runtime sequence
Runtime Decision Sequence
Compatibility-Layer Path
Some non-native clients require a governed compatibility layer before BeaconGuard evaluation. That layer normalizes request shape and context into the structure BeaconGuard evaluates. It does not originate policy decisions. It does not weaken fail-closed behavior. BeaconGuard still performs the deterministic allow/deny decision and emits reviewable evidence.
Enforcement Boundary
Applications do not need to embed AI governance rules in business logic. BeaconGuard places governance in a dedicated boundary where deterministic policy decisions remain consistent regardless of model behavior or prompt drift.
Deterministic Decision Path
For equivalent request state and policy snapshot, BeaconGuard returns equivalent decisions. This is the foundation for operational confidence, incident response, and reproducible reviews in financial workflows.
Compatibility normalization occurs before BeaconGuard policy evaluation when needed. It is not a replacement for the deterministic decision path.
Input and Output Governance
Inputs require explicit context (actors, requested action, attributes, policy identity), so decisions are traceable. Outputs remain constrained to a minimal set: decision result, policy identity, and reasoning context.
Evidence at Runtime
- Evidence is emitted as structured records, designed for audit and investigation.
- Failure conditions are explicit rather than implicit.
- Decision provenance stays attached to policy identity and input context.
Reviewer Focus
A reviewer should confirm that the request path is normalized before evaluation, that policy evaluation produces deterministic allow/deny outcomes, that malformed or missing inputs fail closed, and that each execution decision writes reviewable evidence before model calls can occur.
Decision and Review Loop
A control outcome is produced before execution; allow moves to bounded model interaction, deny blocks by fail-closed policy, and each outcome is retained as decision evidence.