System Architecture
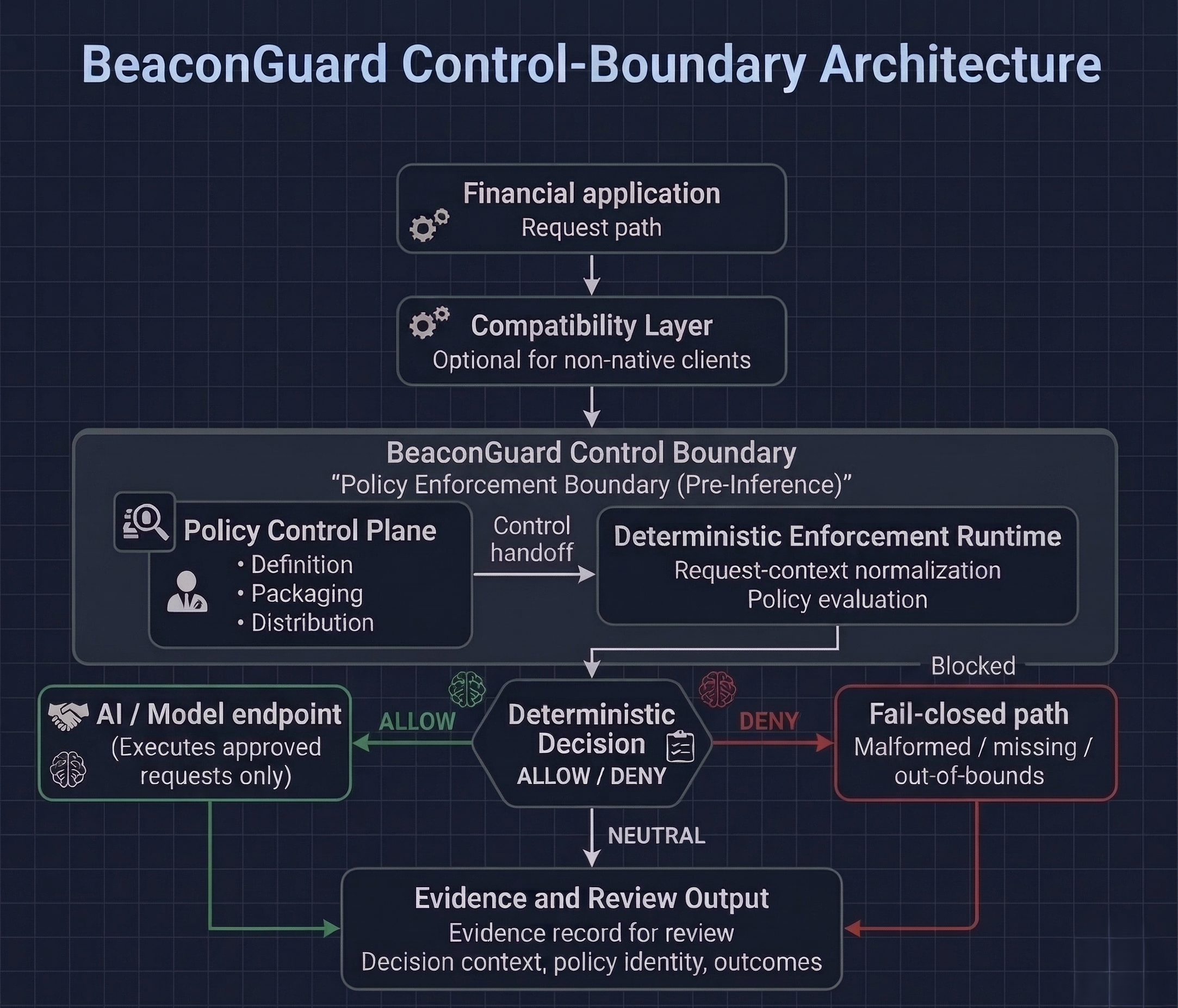
BeaconGuard inserts a deterministic policy and evidence boundary between enterprise applications and AI/model endpoints. The architecture separates policy definition, runtime enforcement, and reviewable evidence output so control decisions stay explicit and bounded.
What this diagram shows
The diagram shows the control boundary between your application and AI/model endpoint, the major components that shape runtime policy control, and the enterprise trust domains across those components.
It clearly separates static structure from runtime sequence: components and trust zones are fixed by design, while allow/deny outcomes are determined at execution time.
The evidence path is shown as a review stream that follows policy decisions for security, risk, and audit visibility.
Reviewers should verify where BeaconGuard is invoked: request context enters the control boundary after application shaping, policy decisions are made inside the boundary, and only approved traffic exits toward the model path.
Policy control plane
Defines and distributes policy inputs for BeaconGuard enforcement. It is where enterprises manage control intent, not model behavior.
Deterministic enforcement runtime
Applies policy in the request path and returns explicit allow/deny outcomes with context for every authorization decision. If request context is malformed, missing, or out of bounds, BeaconGuard fails closed.
Evidence and review layer
Captures structured decision evidence so review teams can reconstruct control outcomes during review and incident analysis.
Trust boundaries
- What enters BeaconGuard: request context, policy intent, and required authorization signals.
- What BeaconGuard decides: deterministic allow/deny with explicit decision context.
- What proceeds to the model endpoint: only requests that pass policy and context checks.
- What is emitted for review: structured evidence of decisions, policy references, and rationale for governance visibility.
Compatibility layer for non-native clients
Some applications and clients do not natively produce the request structure BeaconGuard evaluates. In those cases, a governed compatibility layer may sit before the BeaconGuard control boundary.
Its job is to normalize requests into the BeaconGuard path. It is not a policy engine. It is not a bypass around fail-closed behavior. Evidence and review output still belong to BeaconGuard’s control boundary, not to the compatibility layer.
Reviewer checkpoints
- Confirm the placement of the boundary relative to transaction, analyst, and service logic.
- Confirm policy inputs are versioned and auditable at enforcement time.
- Confirm fail-closed behavior is explicit for malformed, missing, or out-of-bounds request context.
What BeaconGuard is not
- BeaconGuard is not the system of record.
- BeaconGuard is not the transaction processor.
- BeaconGuard is not the model host.
- BeaconGuard is not the application UI.